For those of you that were wondering, SQL Server isn’t the only platform which can be attacked via a SQL Injection attack. Apparently the MySQL.com website which hosts the official distribution channel for the MySQL database platform was attacked using good old SQL Injection earlier today (notice sent out via seclists.org including their schema).
Often I hear from MySQL professionals that MySQL isn’t susceptible to SQL Injection attacks. Apparently not only is it susceptible to SQL Injection attacks, but the company that writes the MySQL engine can’t correctly secure their website from being attacked. According to sucuri.net the “customer view application was used as the entry point, where the attackers were able to list the internal databases, tables and password dump…”. Not only was the password dump captured and posted only, but people have begun cracking the passwords, and some of these passwords are stupidly simple. The account sysadm (which I assume is pretty important) has a password of “qa”.
Apparently the Director or Product Management (who has 20+ years experience with most database platforms) used a 4 digit numeric password (probably his ATM pin code) as his password.
Needless to say, if you have an account on mysql.com and you use that password anywhere, you should probably change that password anywhere else that you use it.
If you think that your application is susceptible to SQL Injection attack, I recommend chapter 6 (SQL Injection Attacks) of “Securing SQL Server” which talks about how to prevent SQL Injection attacks. The examples which I provide are not SQL Server specific and the techniques shown to prevent SQL Injection attacks can be used against pretty much any relational database platform.
Denny
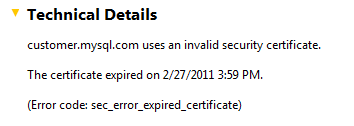
UPDATE (1pm PST 2011/03/27): Apparently the SSL certificate for logging into the MySQL.com website expired a month ago. The reason that I found this was that I was going to try and log in with my normal passwords (I’m pretty sure I have a mysql.com account) but with this error message, I’m not so sure about that. It’s probably OK, but still…